I cannot believe that it has been five years since we officially went live with Workday Student. I am often asked if Workday Student has all the functionality one needs. Sometimes a few who have not yet implemented Workday will make a statement like “Workday Student doesn’t have all the functionality we need”.
Let us face it, no SIS has everything one needs, period. And to expect them to do everything everyone of us wants is unrealistic expectation. This is precisely why, we surrounded systems like Banner and PeopleSoft with several other products. And customized these products in ways that came to bite us when major upgrades were rolled out.
For us, even with Workday, we continue to have some of the additional systems, but less than before and we have successfully adopted a lot of the native functionality of Workday. Using its excellent integration methodology we have increasingly centralized a lot of information that were non existent or were all over the place. And by using its low-code programming platform, Workday Extend, we are moving more and more of the functionality that were externally programmed. Doing so presents the users with a unified interface like the native Workday. In addition, the product is supported and has followed the rest of Workday when it comes to upgrades – the applications work for the most part and if changes are likely to affect them, you have sufficient notice to fix them. Finally, we have built the student datawarehouse using Workday Prism. Such centralization, I don’t have to justify, has clear advantages and lessens the total cost of ownership.
I would like to share our experiences with the hope that it helps clarify what are the capabilities of Workday Student that have worked out well for us. Because of the length, I am splitting it up in multiple posts.
(more…)
To follow up, I probed Gemini further. I will spare you the questions I asked, but show you the result. I asked Gemini to plot the total cost of 8 gallons of gas at the local station, at Costco assuming it is 20 cents a gallon cheaper, and the total cost at Costco including the driving cost and the net difference for price – all ranging from $2.75 per gallon to $3.50. I wanted these plotted in a graph and presented as a table.
(more…)
On Sunday, I stopped by a gas station near our house. I looked on Costco app and found that at the closest Costco gas station, about 20 miles away, cost 20c per gallon less. My 2023 Corolla Hybrid has the capacity for about 8 gallons and it gives me around 40 miles per gallon. I could have easily calculated whether it is worth filling up locally or to drive to Costco. Of course, one never drives to Costco just to get gas and I end up buying things I really don’t need. Thats a different story.
So I engaged with Gemini, the rebranded Bard from Google. I want to warn you that this is a long post, but an interesting one 🙂 What follows is a conversation, which is the. power of these tools and not one where you ask something and expect an answer right away. Please follow the back and forths below. (more…)
Happy New Year to All. As one of the IT leaders of an institution that was an early adopter, I have thoroughly enjoyed our relationship with Google. There was a time in the past when Google paid special attention to Higher Ed and we developed some strong professional connections, some of which continue to date. Most of the folks we knew have moved on and privately they would tell me that the reason for the move is that the current Google is not what it used to be. Totally understandable, because this is what happens to corporations and they have constant financial pressures and they have to make changes. But, frankly, this should not be at the expense of loyal and long term customers like Higher Eds and K-12s!
Our current issue with Google support has to do with Gmail and Photos showing the total storage usage of the domain on each user’s account, instead of their individual storage usage. Photos also displays a red warning bar at the top due to our domain having less than 20% of storage left in our newly enforced domain storage limit. It has taken six days of numerous techs and emails to finally get them to understand that it is a bug and not a user, account, or browser display issue. They have finally escalated it to their engineering team but with no ETA on resolution. But to get to this, I would like to share some back story (pretty long), so, please hang in with me.
As you know, Google initially provided free services to K-12 and Higher Eds. We were told that the founders strongly believed in giving back to educational institutions that had a strong role to play in making them who they were. We would repeatedly ask if this is a sustainable model and we were repeatedly assured yes, nothing to worry, because, look, even after giving you all these services free, the company is still financially flourishing. And part of this deal was that we didn’t have to worry about how much data we are storing in Google.
The thing about Google was, pretty much everything just worked! Initially at least, there was no concept of “Google support”. Services were free and we basically were on our own and consulted their documentation when we needed help. But there were multiple groups we network with who are Google customers and we relied on each other for assistance. When there were some catastrophic failures, we contacted our Higher Ed contact in Google directly for assistance and they internally escalated these. Obviously, we all know now that this was not a sustainable model.
But in the past 5 years or so, we were directed to seek help from Google support. Google has been rolling out a lot of new features and our need to rely on trusted sources has been increasing. So, I would say, our reliance on Google support has been steadily increasing over the past 5 years. Our overall experience with Google support has been dismal.
Why? Because many support folks responding to our tickets simply do not understand what the issues are and provide canned answers. I get the feeling that they do not understand the Higher Ed environment and issues. We need to escalate many of our tickets multiple times to get to someone who understands and answers our question and pray that they will be reachable if needed. Many times you are so frustrated that you simply give up, if it is some new feature that you want to adopt! We revisit such a list of unfinished new features adoption often! This is NOT how this is supposed to work.
In 2021, Google dropped a big bomb! Specifically read the section “Introducing a new storage policy”.
- “we’ve grown to serve more schools and universities each year, storage consumption has also rapidly accelerated” – Understandable
- “Storage is not being consumed equitably across — nor within — institutions, and school leaders often don’t have the tools they need to manage this” – Well, when you had told us that everyone has unlimited storage, it is natural for this to happen, so why is anyone surprised? And we didn’t have any tools to manage it because you, Google, never provided any!
- “… we will be implementing a new pooled storage model and helping admins and school leaders manage their storage. Nothing is changing today and we expect that more than 99% of institutions will be within the pooled storage provided by the new policy.” – We all appreciated that we had some time to deal with this! Thank you Google for being somewhat considerate.
- “The new storage model will provide schools and universities with a baseline of 100TB of pooled cloud storage shared across all of your users” – This is the kicker because we have a LOT more. I guess we are in the 1%!!!
Why is this a problem for us?
- Coming up with a single number to apply across everyone is easy and convenient for Google, but for a company that takes pride in data analysis, this is SO flawed.
- We argued that Google should set these limits based on additional criteria, one of which is how long a customer has been using their unlimited storage offer.
- When you gave away unlimited storage (and marketed it heavily) and did not provide any tools to monitor usage, you basically encouraged certain behavior on the part of our users. Google folks used to proudly say “You don’t have to delete anything! Use search to find stuff!”
- Secondly, we understand that this has resulted in an uncontrolled use of resources and something needs to be done and I am truly thankful that they gave us a couple of years to deal with it. But 12 years of accumulated content is way too much to trim down to 100 TB.
- Every single method we came up with was met with use cases where our plans to delete would be highly disruptive. For example several graduated students still had data from research they did as an undergraduate that their faculty mentor and their group continues to access. As a result, we cannot simply delete a departed student’s drive files. Same thing with employees.
- So we asked Google if we can archive most of the older files that can be retrieved when needed. Long story short… they paraded a bunch of vendors, but no one had a solution. Because Google Docs, Sheets and the associated metadata (such as who it is shared with and version history) are proprietary, you cannot use other systems to backup and restore and Google itself has no solution to this. Believe me, Google Vault is Not a solution to this since it does not store sharing or folder structure data.
Understandably, we are too small to win any argument with Google, so we launched a campaign to try to cut down storage, but we were not that successful. And we will continue this. But, we ponied up money and purchased additional storage from Google recently. Whereas it may appear reasonable, it really is not. As I mentioned earlier, I would much rather archive a lot of what we have and not have them in expensive active storage. Amazon Glacier or Google Cloud storage would be perfect, but I cannot move them there in their native format! And this is NOT my fault and Google is asking me to pay for this.
Google also has been rolling out new tools to help us manage the storage. So, here we are, we have purchased additional storage. Since we only purchased enough for what we predict to use this year, we are using over 80% of our storage, which creates a warning message on some apps. This is useful for admins, but the current bug shows this warning for all our users in Photos.
We created a ticket 6 days ago and received replies from a different support tech each time, none of whom understood the issue and gave us steps to try that did not address the actual bug!! After bringing this up with our account rep and finally getting a tech that understood it, six days later it has finally been accepted as a bug. And there is no ETA for a fix. In the meantime, we are getting cases from our users worried that they are over quota and confused because they know they aren’t. This is so frustrating on many fronts.
If this had happened when the services were free, my approach to this would have been very different from now, when we are paying for services! And the frustration is compounded by another episode with the Google Account team and reseller of Google services recently that I will write about later.
As I began this, this is not the Google we were used to. Period.
In case you did not see this, On October 30, 2023, President Biden issued an Executive Order on the Safe, Secure, and Trustworthy Development and Use of Artificial Intelligence. AI is already being used in a variety of ways on college campuses, from teaching and learning to research and administration. I am pretty sure that the executive order will have implications for us in higher ed.
One of the key goals of the executive order is to promote the responsible and ethical development and use of AI. This is important for us because these systems are as good as their training datasets and therefore likely to amplify biases and inequalities in the training datasets and the corpus of information they continue to learn from. For example, if an AI system is used to grade student essays, it could be biased against certain groups of students, such as those from underrepresented minority backgrounds.
(more…)
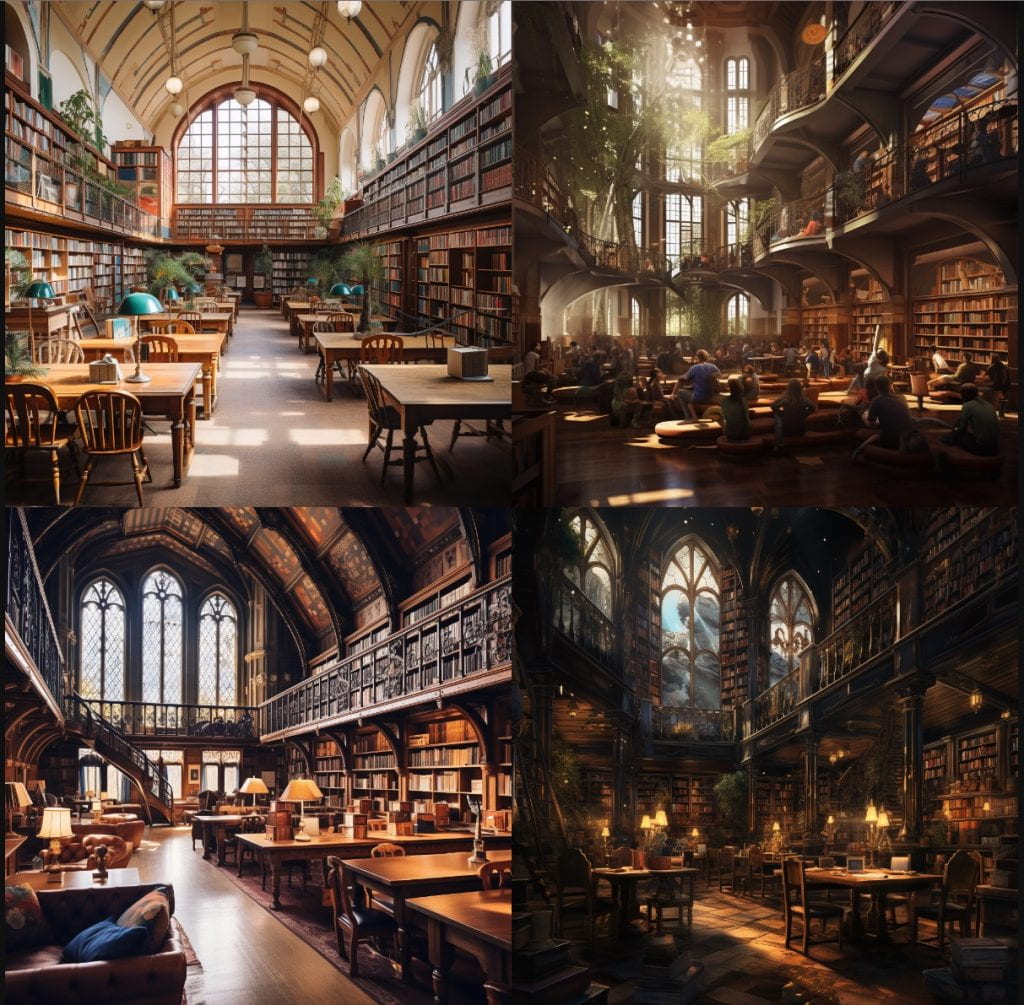
AI and Art
I continue to play with AI tools and am having fun. I am playing around in Midjourney asking it to imagine various things in the future. I would say they are pretty interesting, but not sure how accurate these predictions are. For example I asked it to imagine how a library in a small liberal arts college will look in 2035 and this is what it came up with. This is because our Clapp library will be undergoing a renovation next year and it was in my mind. Looks pretty interesting but I can’t imagine Clapp looking anything like this in 2035, on the other hand, how can I be so sure?… I intend to explore it more.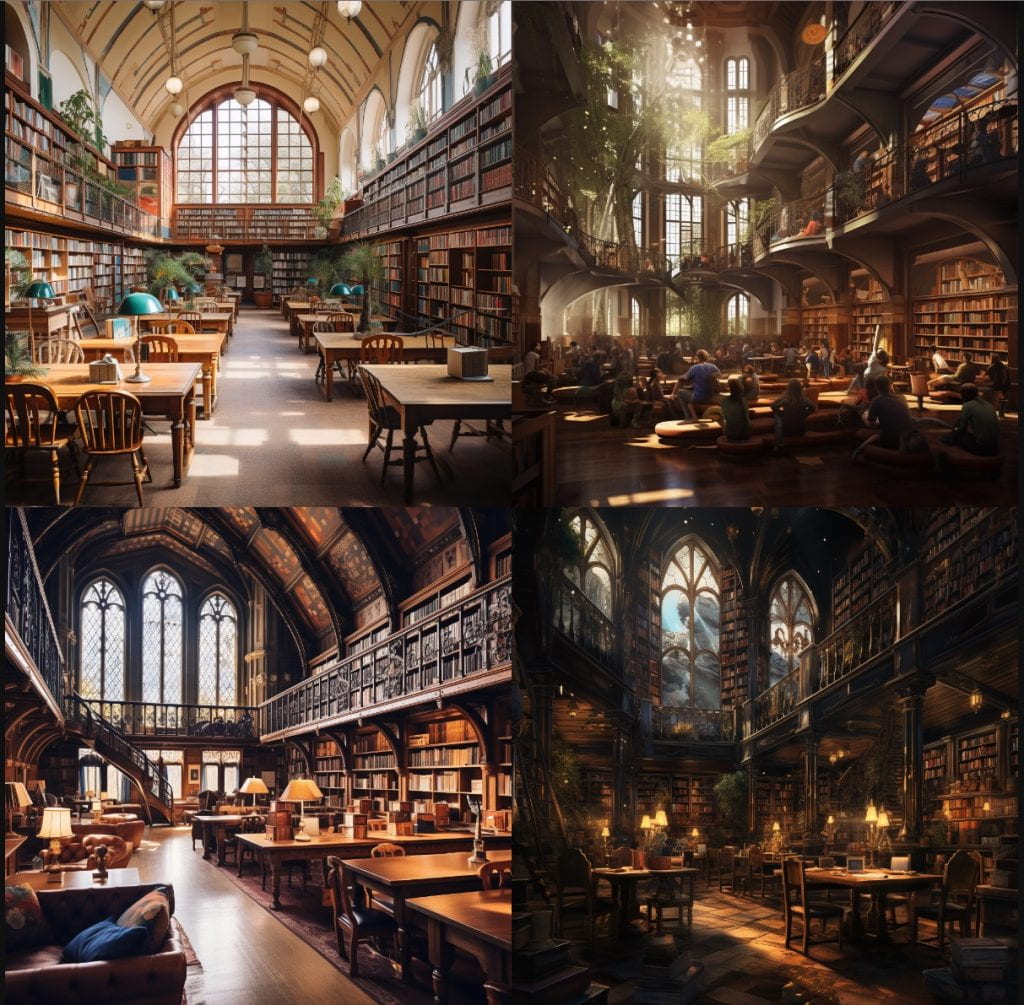
(more…)
I am sure I am not the only one who complains that summer is going by too fast! It indeed seems that way… For me, it all began with a trip to Southern Spain in May, that we thoroughly enjoyed, then a trip to Southern California for a wedding in June and then to Canada for a few days in July. When you travel time tends to go by faster than if you are just hanging out at home. On top of all of this, until mid June or so, the temperatures were not the usual warm ones, instead they were pretty cold.
I have been learning a lot more now by engaging with ChatGPT and Bard than simply asking my phone questions by saying “Hey Google” and asking random questions. For example, the hard work of planting some vegetables by my wife in our garden hasn’t yielded much this year. When I probed the AI tools, I learned that when the temperature is colder than normal this happens. They cite many reasons including the fact that the bees don’t come out when it is colder to pollinate the flowers. Got it. Could I have found this out through Google search, yes, but through multiple steps for which I don’t have time 🙂
(more…)
Another Academic Year ended and it has gone way too fast! Most of my and several of my staff’s attention has been on the upcoming Clapp Library renovation. We were off to a quick start last July, but then had to pause in December because of budget issues. Then we spent the first three months this year preparing programmatic enhancements ideas for the Trustees, which was approved in April and we have been back to the intense design phase, which is fast coming to a close. Now starts the real work of planning the move! We are excited and well prepared. Stay tuned.
I came back last Monday after a week in Southern Spain. My family and I rented a car in Madrid and drove to Cordoba, Granada, Malaga, Cadiz, Arcos de la Frontera, Seville and back to Madrid. It was a fantastic trip with so many things to see, but I was expecting to see more Moorish things than we were able to see. Food was a bit bland for my taste, but there were always the add ons 🙂
(more…)
I am on my way to California to attend a two day gathering of Higher Ed leaders. It was approximately 3 years ago when COVID struck us big time, caught us unawares and all hell broke lose. I admire the swiftness with which the senior administration at Wellesley took action. Having a respected physician, Dr Paula Johnson, as the president helped and especially her leadership in a group of Higher Eds in Massachusetts.
I am also very proud of the fact that we, in LTS, are one of the very few organizations who decided to take on the technology responsibilities needed to support our COVID testing and related matters without needing a paid vendor solution. And I think we did a great job and by making the right choices, we saved the College money and served our community better. What we did was a tremendous amount of work and describing all will take a long time, so I will describe just a few highlights here.
(more…)
NERCOMP Annual Conference is one of my most favorite conferences. It provides an excellent way to meet colleagues and network and exchange ideas. The number of attendees is just right for you to be able to touch base with a fair amount of colleagues during the two days the conference is held.
I will discuss a few things related to the conference here, but I encourage you to read my tweets during the conference.
I participated in a preconference panel “Cloud Transformation: Before and After” along with colleagues from Bentley College, Smith College, Barnard College and Simmons University. Most conversations revolved around our experiences implementing Workday and most attendees are in the process of implementing or are on the verge of making a decision. It was fun, but based on what I heard from some of the attendees, it was a bit too long. I agree, 4 hours is kind of long though we had a break in between. We need a half time show like Superbowl to wake people up 🙂
(more…)